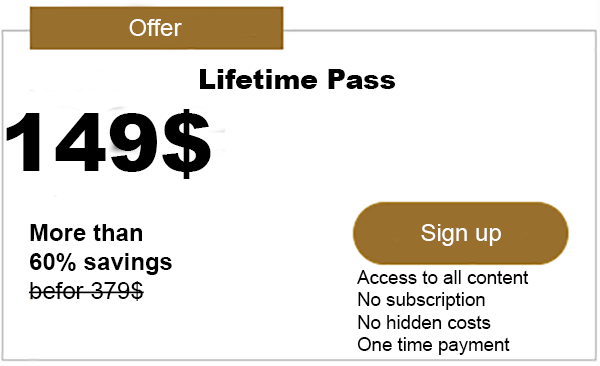
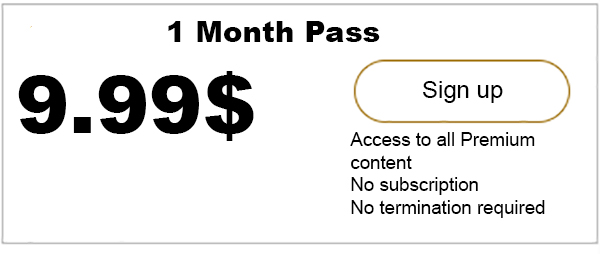
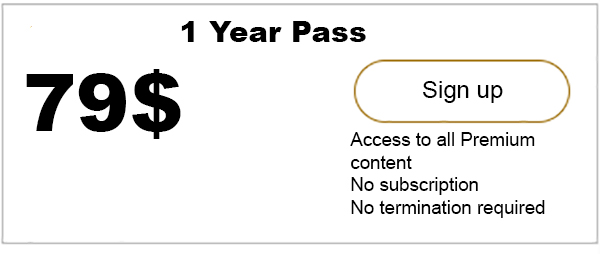
Advertisment
This past June news.Bitcoin.com reported on a demonstration that took place at the world famous hacker conference in Las Vegas, Def Con 25, which claimed to show the audience how to break a bitcoin hardware wallet. Now according to a recent blog post, the presentation revealed to attendees found glitches in a Trezor that revealed…

Bitcoin.com is author of this content, TheBitcoinNews.com is is not responsible for the content of external sites.
Our Social Networks: Facebook Instagram Pinterest Reddit Telegram Twitter Youtube