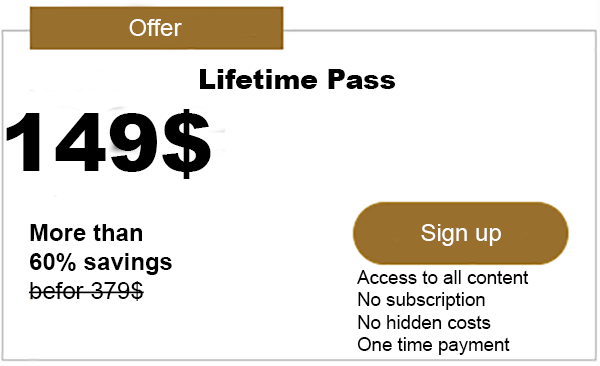
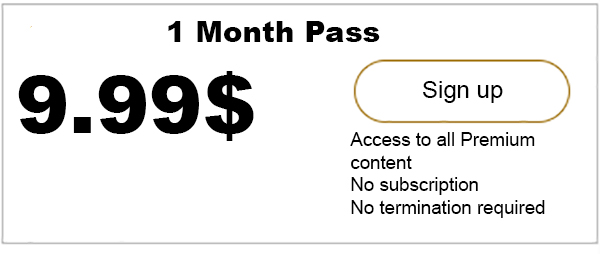
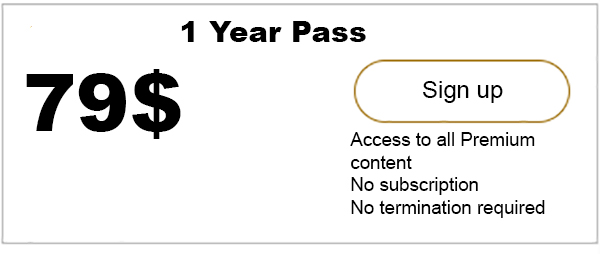
Advertisment
In today’s blog post we will take a closer look at one of the core concepts of IOTA and any crypto currency, namely public key cryptography and digital signatures. In IOTA, in order to transfer tokens from one address to another, you create a transaction. A transaction contains information about the payer, the receiver, and…

iota-news.com is author of this content, TheBitcoinNews.com is is not responsible for the content of external sites.
Our Social Networks: Facebook Instagram Pinterest Reddit Telegram Twitter Youtube