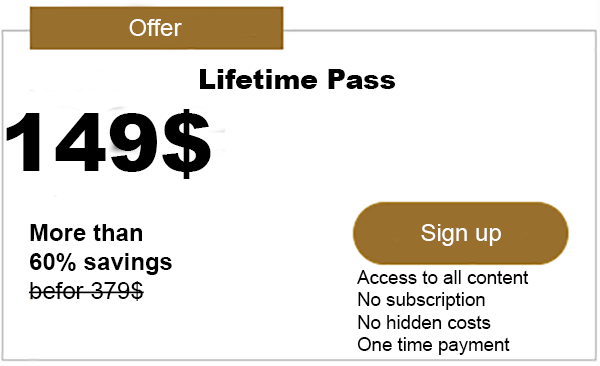
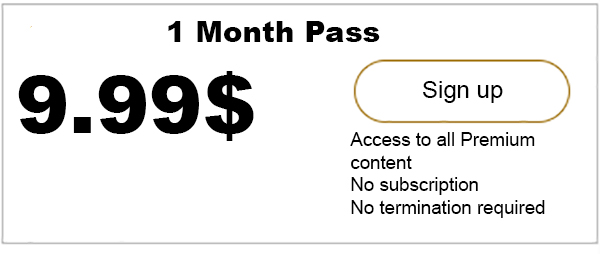
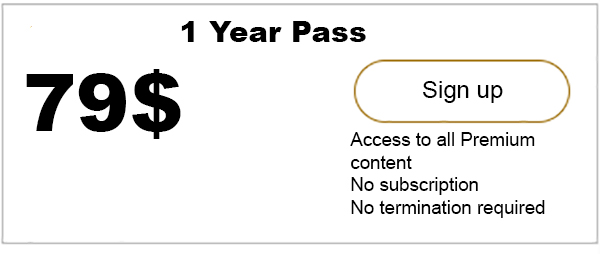
Advertisment
Introduction The evaluation of the origin of a product, i.e. the identity of its manufacturer, is an important matter for many industrial and commercial sectors. Preventing the illicit exploitation of established brands in which market and profit are taken is not the only objective of anti-counterfeiting. Even more important is to protect the final purchaser…

iota-news.com is author of this content, TheBitcoinNews.com is is not responsible for the content of external sites.
Our Social Networks: Facebook Instagram Pinterest Reddit Telegram Twitter Youtube